denial of service (DoS)
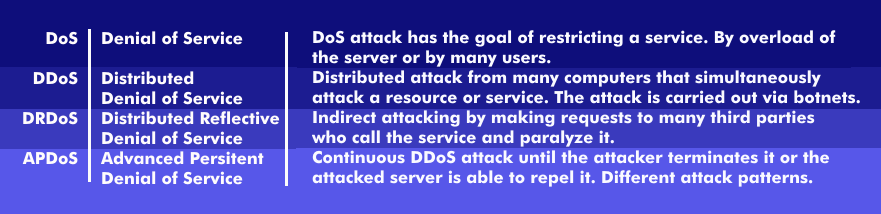
Denial of Service (DoS) are denials of service that cause web services to be compromised on the Internet and, when executed as a DoS attack, can take an attacked server or website out of service.
DoS attacks are triggered by server overload attacks, such as bombarding a mail server with a flood of mail, sending millions of requests to a server, or flooding a network with data packets. In all cases, the functions can no longer be adequately executed due to overload of the servers or networks. The servers are no longer accessible, the networks can collapse.
DoS attacks usually do not target access to the network, system or data files, but aim to restrict, block or render a service unusable. For this purpose, the available programs or network resources are extraordinarily overloaded, sometimes collectively by thousands of users.
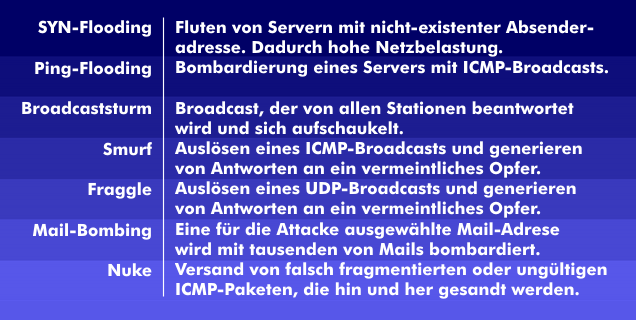
A DoS attack can be prepared by IP spoofing. To do this, the attacker uses an authorized IP address to gain access to the system or network, and then executes his DoS attack. Besides mail bombing and broadcast storm, other DoS attacks include SYN flooding, ping flooding, ping of death( PoD), smurf attack, nuke attack, teardrop attack, distributed denial of service ( DDoS), distributed reflective denial of service ( DRDoS) and advanced persistent denial of service ( APDoS).
SYN flooding involves overloading a server and causing it to crash. Ping flooding, on the other hand, is about severely impacting the performance of servers, and smurf attacks target networks that use pings. Also interesting are teardrop attacks aimed at reassemblingTCP/IP fragments and, above all, DDoS attacks, which are triggered simultaneously by several computers working in a network, such as botnets.